POWERFUL SECURITY
The perfect solution for battery protection

BRAND REPUTATION
Fake batteries hurt the corporate bottom line beyond just the profits lost to the illegitimate devices, they can also destroy brand reputation by delivering poor performance or even causing personal damage to the end users.
In the new era of cordless consumer applications, long-life efficient and safe batteries are key significant differentiators for device makers. When replaceable, the same efficiency and safety are expected by customers. The device warranty is also often limited to the replacement by approved battery packs. This is a matter of brand image.
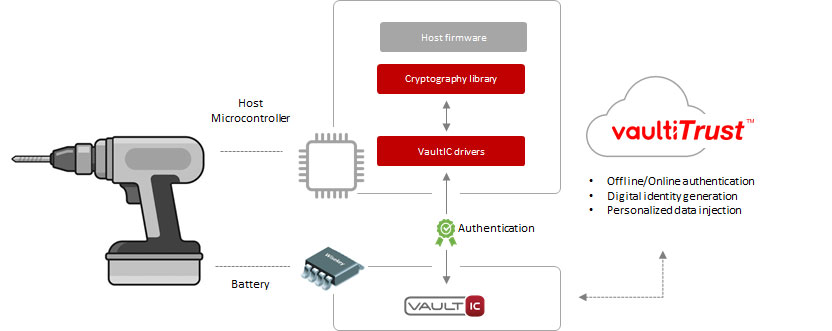
Battery authenticity is not easy to check. Traditional physical methods have proven their limits. Digital security based on cryptography and electronic signatures offers a robust way to verify the identity of a battery pack. When affixed to the object, the secure element acts as an ID Card that can be reliably checked by the host device before allowing any action.
With the combination of secure hardware modules, trusted identity software, and design customization services, the WISeBattery platform is ideally suited to defend your products and your brand.
HOW IT WORKS
WISeBattery VaultIC
The VaultIC® security module embeds a complete firmware dedicated to IP protection and anti-cloning.
This firmware uses a variety of cryptographic mechanisms such as digital signature generation/verification to provide a number of protection and authentication functions. The VaultIC183 and VaultIC186 are specifically designed for battery digital authentication.

| VaultIC183 | VaultIC186 | |
|---|---|---|
| Hardware Security | CC EAL4+ level | CC EAL4+ level |
| File System | 1.5KB | 1.5KB |
| Communication | I2C | OWI |
| Cryptography | ECC up to 283 bits | ECC up to 283 bits |
| Certificate | v (+ Host Pub Key Mngt) | v (+ Host Pub Key Mngt) |
| Open Detection | x | x |
| One-Tap Authentication | x | x |
| KeyPair Generation | v | v |
| VaultiTrust Provisoning | v | v |
| Packages | Wafer, DFN6 | Wafer, DFN6 |
| Operating Ranges | [1,62V; 5,5V] [-40°C; +105°C] | [1,62V; 5,5V] [-40°C; +105°C] |
| Status | Production | Production |
| datasheet download | datasheet download |
DESIGN CUSTOMIZATION SERVICES
When it comes to providing robust digital security solutions to authenticate batteries, to guarantee safety and to protect brand’s reputation and revenue, WISeKey offers a rich portfolio of hardware secure elements, embedded firmware and drivers, together with a complete architecture proposal. This is available to you as a standard proven turnkey system. WISeKey also offers more than 40 years of expertise in digital security at your service to design custom solutions. We can help you define and implement the best security system architecture for your application. We can also customize our secure elements or develop specific firmware to allow a seamless integration of our digital security into your device.
WISeArchitect
Custom security architecture design:
- Device-to-Host authentication applications
- Support from specification to deployment

WISeDeveloper
Custom security firmware & software development:
- From FW & SW customization to full custom development
- From Chip-to-Server



COMPLETE TRUST SERVICE
Secure data generation and injection into secure elements is at the heart of many connected systems such as Internet of Things, anticounterfeiting, battery protection or traceability of goods. WISeKey presents VaultiTrust™, a unique comprehensive service to support the deployment of such systems. VaultiTrust takes advantage of WISeKey’s government grade security certified premises and end-to-end digital security management to, for instance, generate keys and efficiently install them into chips. A web portal complements the service by offering an easy way to configure, manage and track production.
With VaultiTrust, the managed data can be static (same for a whole batch of chips), dynamic (unique per chip) or security related (keys and digital certificates). This is all configured through the web portal.
